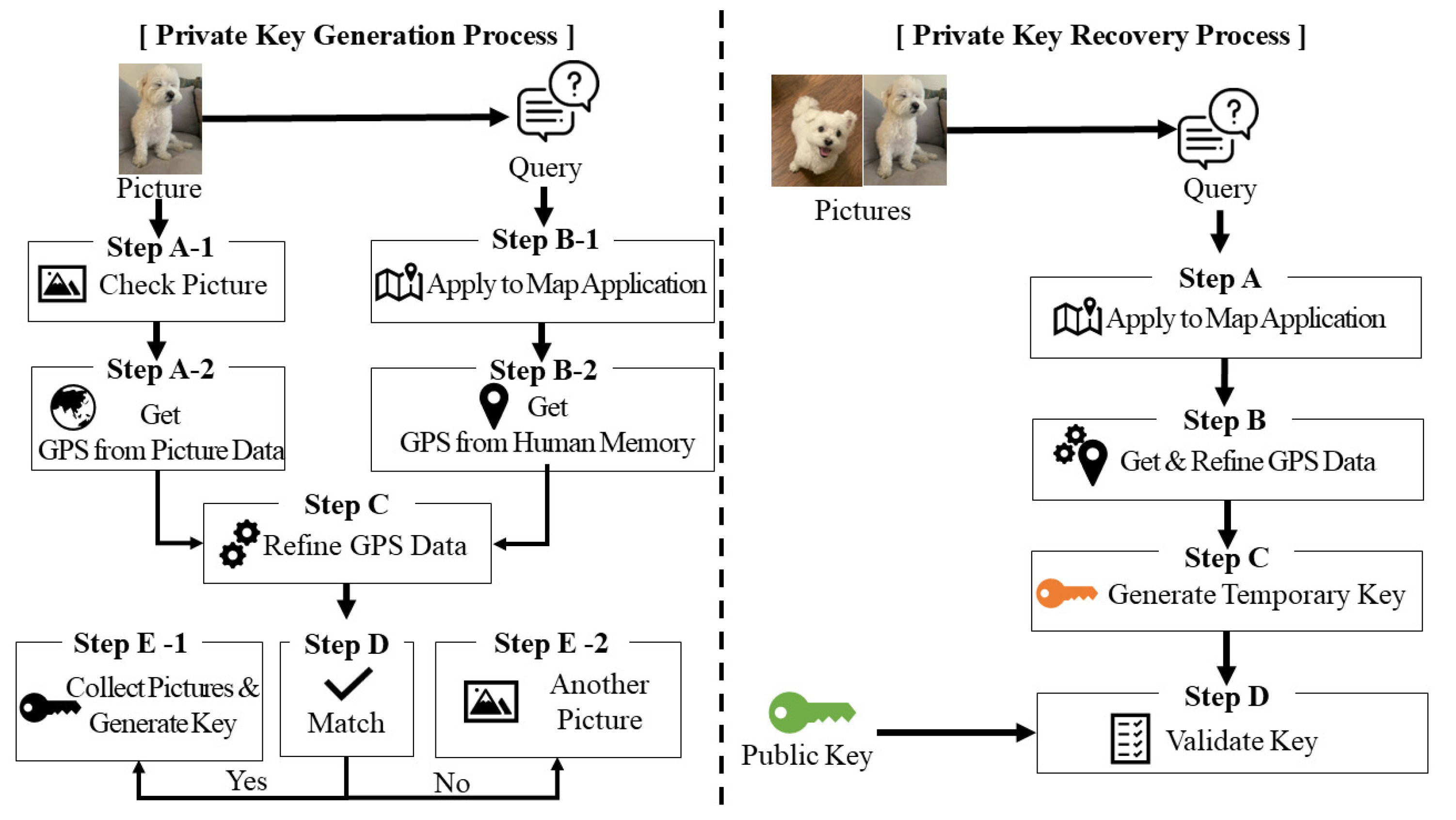
Mathematics | Free Full-Text | Reminisce: Blockchain Private Key Generation and Recovery Using Distinctive Pictures-Based Personal Memory

A New Method IBE Interfaced with Private Key Generation and Public Key Infrastructure to Achieve High Data Security | Semantic Scholar
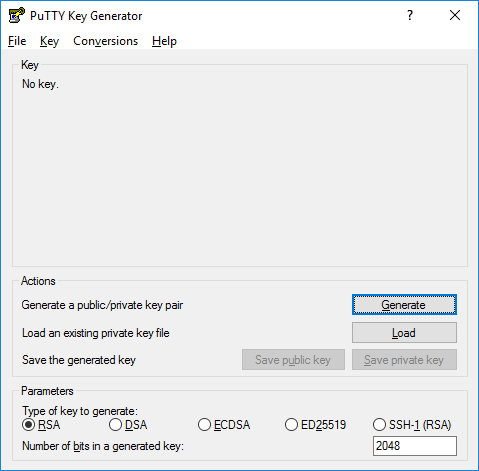
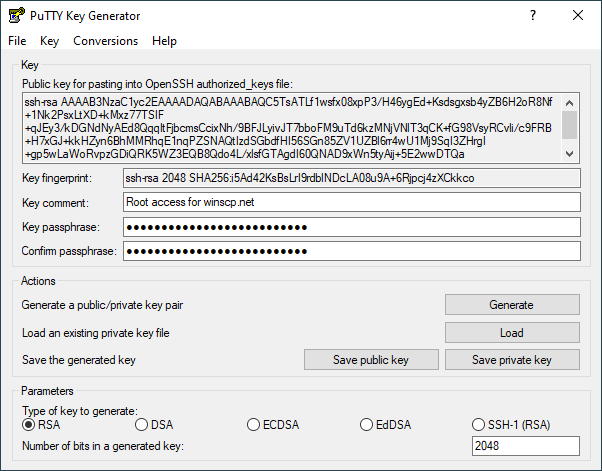
How to install and use puttygen to create new key pairs and change passphrases. Installing keys on server, managing SSH keys.
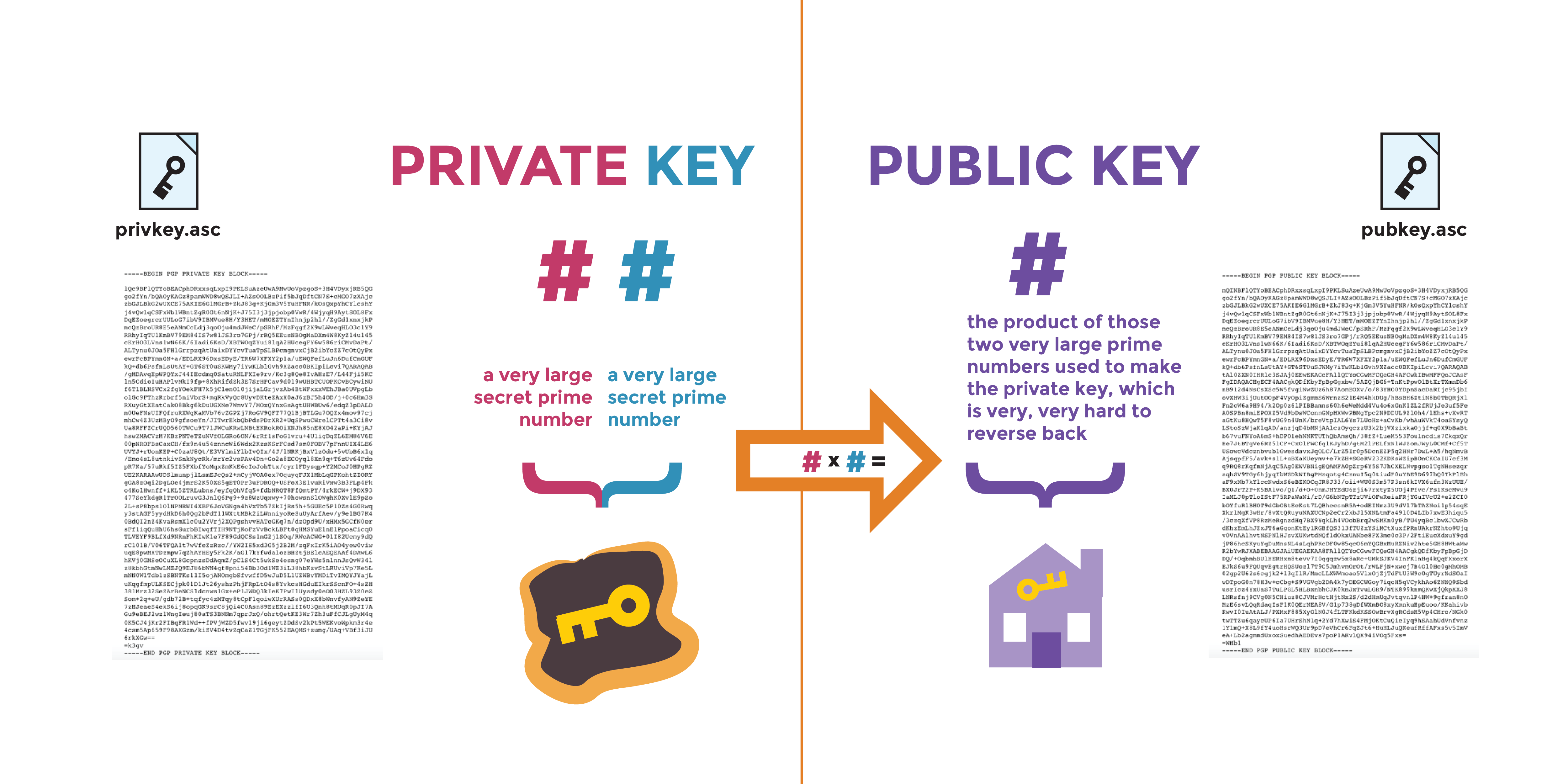
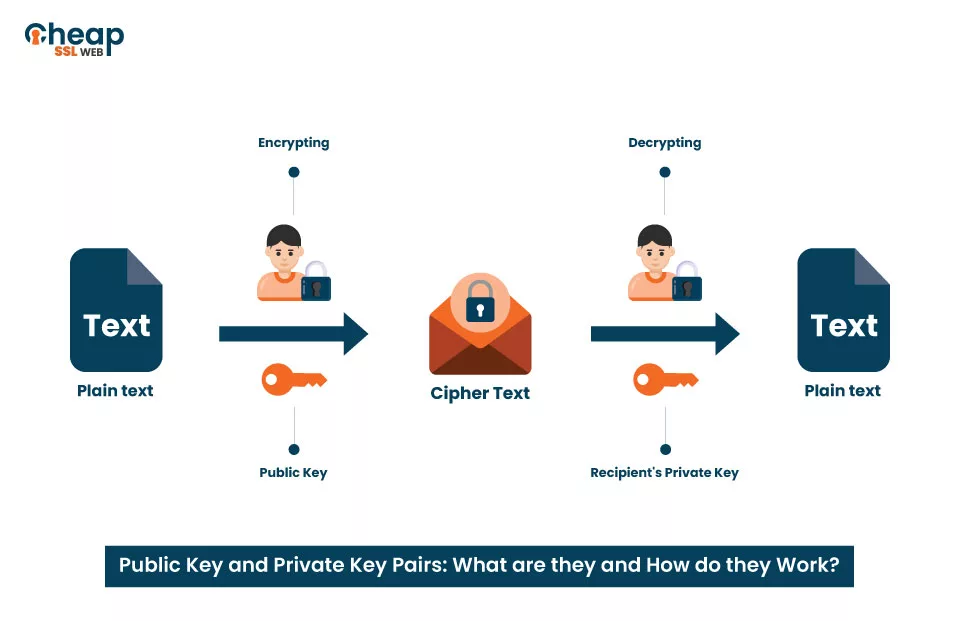
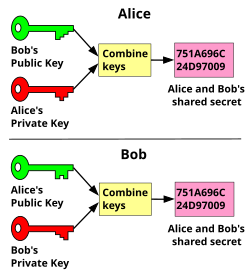
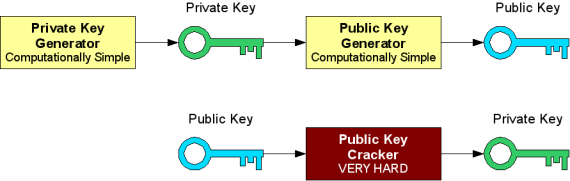
A Deep Dive on End-to-End Encryption: How Do Public Key Encryption Systems Work? | Surveillance Self-Defense